Multi Factor
Complex passwords and better yet, pass phrases just aren’t enough. We can do everything right, use a password manager, unique complex passwords or passphrases, but that doesn’t stop a service provider data breach. With estimates at several billion passwords stolen each year, we can guess that roughly 8 million passwords are stolen daily.
Multi-Factor Authentication – Hackers biggest hurdle
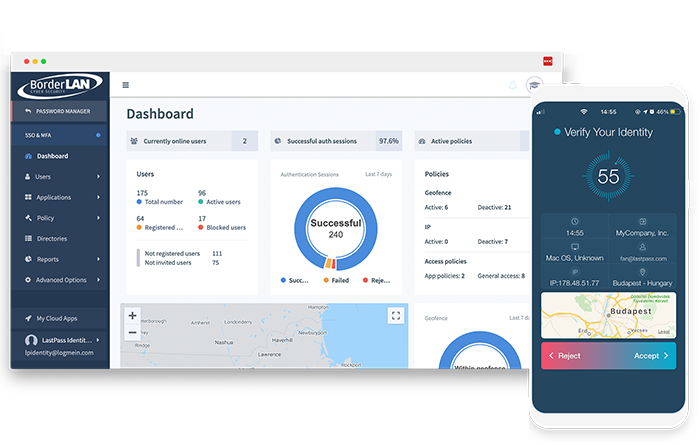
Multi-Factor Authentication, or MFA, is using both something you know (password) and something you have. In most cases the second factor is a one-time password generated either by receiving a text message or an application on your phone. Since mobile numbers can be cloned or stolen, a centrally managed MFA solution is a MUST. Let BorderLAN introduce you to MFA that can be managed centrally by your IT staff. Don’t just hope your employees are using safe practices, know with certainty.
What BorderLAN provides

Leverage biometric and contextual factors to better protect your business while offering a passwordless user experience for employees.
BorderLAN MFA goes beyond standard two-factor authentication to ensure the right users are accessing the right data at the right time, without added complexity.
Adaptive authentication
BorderLAN MFA combines biometric and contextual intelligence to prove a user’s identity with a combination of factors.

Passwordless user experience
Authenticate users seamlessly across all their devices, with a passwordless experience that doesn’t disrupt their workflow or slow them down.

Secure every access point
From cloud to on-premise applications, VPN and workstation, BorderLAN MFA secures every access point to the business.

Customize for your business
Get ultimate flexibility with a variety of MFA methods that can be applied at the user or group level.